A stealthy and modular malware used to hack into Linux devices and build a DDoS botnet has seen a massive 254% increase in activity during the last six months, as Microsoft revealed today.
This malware (active since at least 2014) is known as XorDDoS (or XOR DDoS) due to its use of XOR-based encryption when communicating with command-and-control (C2) servers and being employed to launch distributed denial-of-service (DDoS) attacks.
As the company revealed, the botnet's success is likely due to its extensive use of various evasion and persistence tactics which allow it to remain stealthy and hard to remove.
"Its evasion capabilities include obfuscating the malware's activities, evading rule-based detection mechanisms and hash-based malicious file lookup, as well as using anti-forensic techniques to break process tree-based analysis," Microsoft 365 Defender Research Team said.
"We observed in recent campaigns that XorDdos hides malicious activities from analysis by overwriting sensitive files with a null byte."
XorDDoS is known for targeting a multitude of Linux system architectures, from ARM (IoT) to x64 (servers), and compromising vulnerable ones in SSH brute-force attacks.
To propagate to more devices, it uses a shell script that will attempt to log in as root using various passwords against thousands of Internet-exposed systems until it finally finds a match.
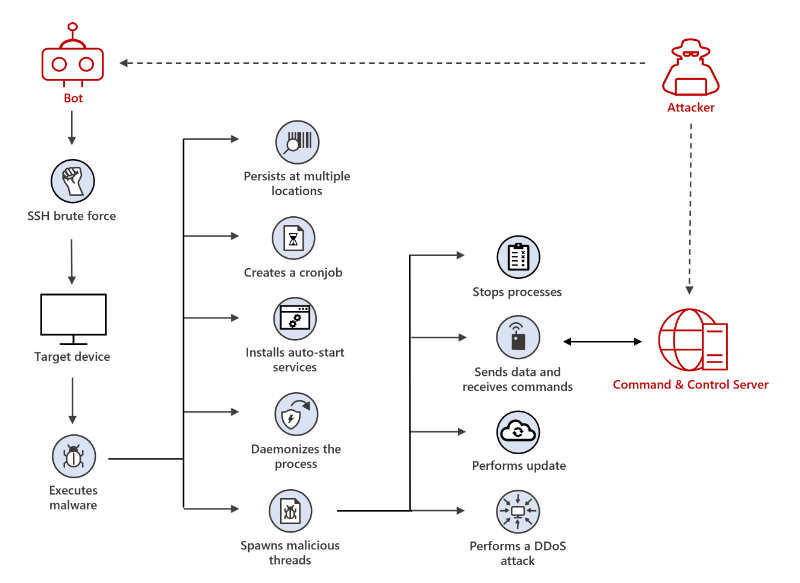
Besides launching DDoS attacks, the malware's operators use the XorDDoS botnet to install rootkits, maintain access to hacked devices, and, likely, drop additional malicious payloads.
"We found that devices first infected with XorDdos were later infected with additional malware such as the Tsunami backdoor, which further deploys the XMRig coin miner," Microsoft added.
"While we did not observe XorDdos directly installing and distributing secondary payloads like Tsunami, it's possible that the trojan is leveraged as a vector for follow-on activities."
The huge boost in XorDDoS activity Microsoft detected since December lines up with a report by cybersecurity firm CrowdStrike which said that Linux malware had seen a 35% growth during 2021 compared to the previous year.
XorDDoS, Mirai, and Mozi were the most prevalent families, accounting for 22% of all malware attacks targeting Linux devices observed in 2021.
Of the three, CrowdStrike said that XorDDoS saw a notable year-over-year increase of 123%, while Mozi had an explosive activity growth, with ten times more samples detected in the wild throughout last year.
A February 2021 report from Intezer also revealed that Linux malware families increased by roughly 40% in 2020 compared to 2019.
Microsoft detects massive surge in Linux XorDDoS malware activity
- aum
-

 1
1


3175x175(CURRENT).thumb.jpg.b05acc060982b36f5891ba728e6d953c.jpg)
Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.