A new version of the ViperSoftX information-stealing malware has been discovered with a broader range of targets, including targeting the KeePass and 1Password password managers.
The report comes from researchers at Trend Micro, who state that ViperSoftX now targets more cryptocurrency wallets than before, can infect different browsers besides Chrome, and is also starting to target password managers.
Finally, the newest version of the information-stealing malware features stronger code encryption and features to evade detection by security software.
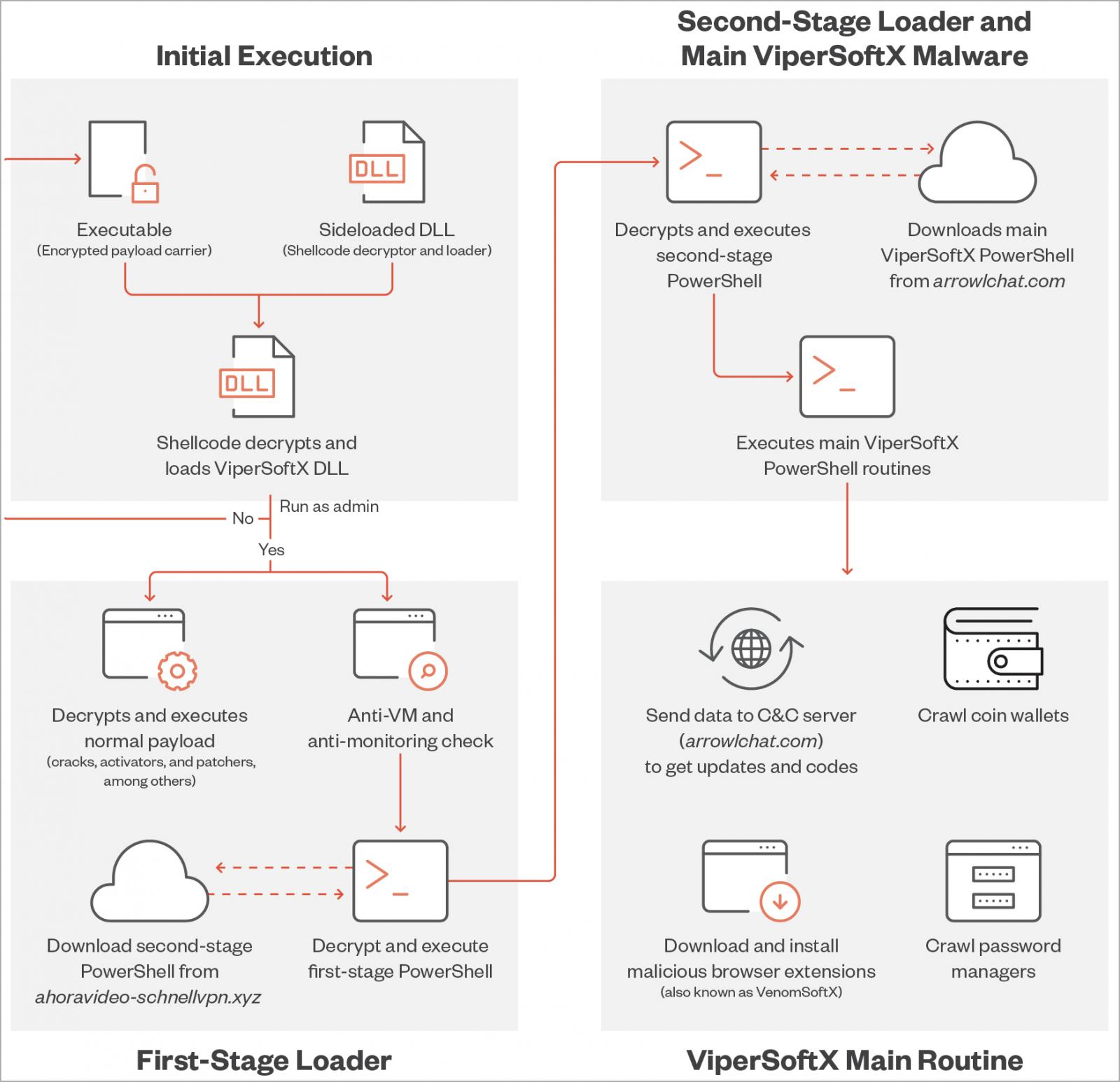
ViperSoftX's latest execution flow (Trend Micro)
Worldwide targeting
ViperSoftX is an information-stealing malware that steals various data from infected computers. The malware is also known to install a malicious extension named VenomSoftX on the Chrome browser.
In the latest version analyzed by Trend Micro, the targeted browsers now include Brave, Edge, Opera, and Firefox too.
The malware was first documented in 2020 as a JavaScript-based RAT (remote access trojan) and cryptocurrency hijacker. However, in November 2022, Avast reported that ViperSoftX was circulating a new, much more potent version.
Avast said at the time that it had detected and stopped 93,000 attacks against its clients between January and November 2022, with most victims residing in the U.S., Italy, Brazil, and India.
This week, Trend Micro reported that ViperSoftX targets both the consumer and enterprise sectors, with Australia, Japan, the United States, India, Taiwan, Malaysia, France, and Italy accounting for over 50% of the detected activity.
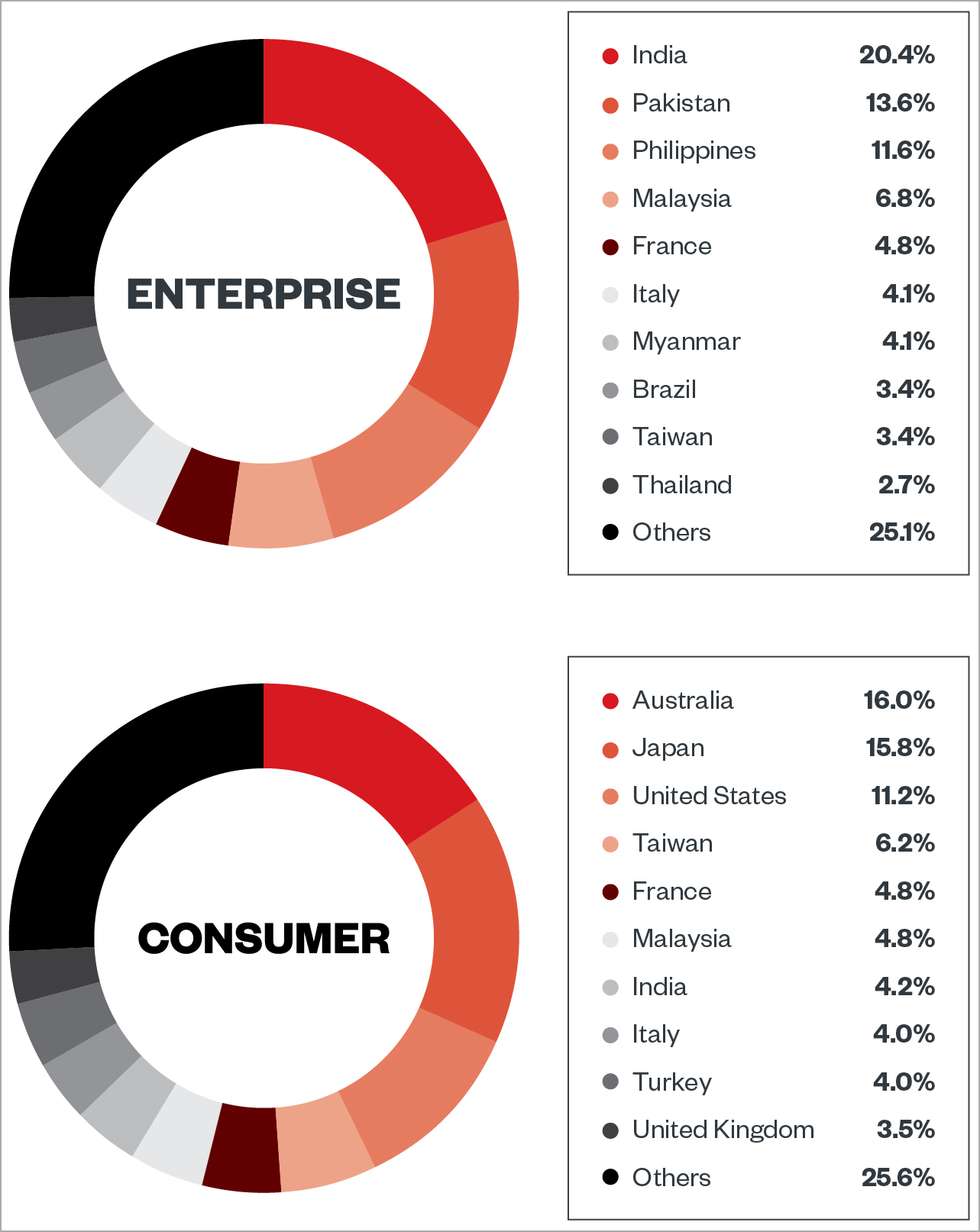
Overview of ViperSoftX targets (Trend Micro)
Based on the analysts' observations, the malware typically arrives as software cracks, activators, or key generators, hiding within benign-appearing software.
Expanded targets
In the version documented by Avast, VenomSoftX targeted Blockchain, Binance, Kraken, eToro, Coinbase, Gate.io, and Kucoin crypto wallets.
However, in the latest variant, Trend Micro spotted increased functionality that steals from the following additional wallets:
- Armory
- Atomic Wallet
- Binance
- Bitcoin
- Blockstream Green
- Coinomi
- Delta
- Electrum
- Exodus
- Guarda
- Jaxx Liberty
- Ledger Live
- Trezor Bridge
- Coin98
- Coinbase
- MetaMask
- Enkrypt
Of particular interest, Trend Micro also reports that ViperSoftX is now checking for files associated with two password managers, namely 1Password and KeePass 2, attempting to steal data stored in their browser extensions.
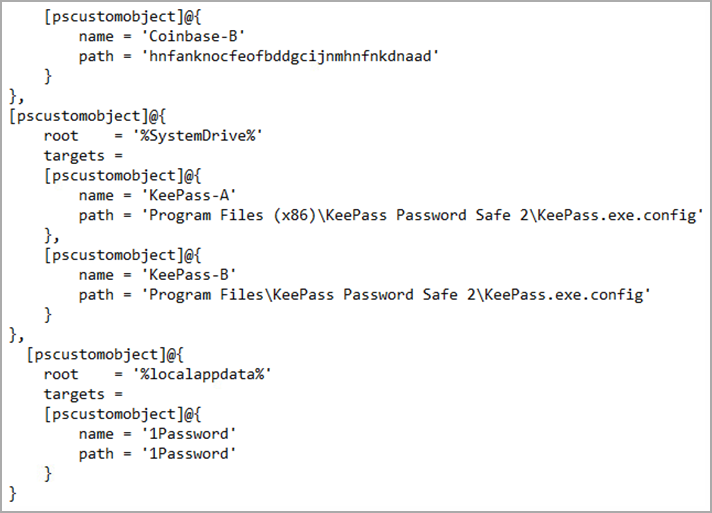
Scanning for password managers (Trend Micro)
The analysts checked if the malware incorporated an exploit for CVE-2023-24055, which allows the retrieval of stored passwords in plaintext form but could not find any evidence of this exploitation.
However, Trend Micro told BleepingComputer that it's possible that if password managers are detected, the threat actors could target them with malicious activity in the later stages of the attack.
"As of the time of the writing, There was no clear detail that we can gather from the codes of the malware except to send the data gathered from getting the configuration files. The KeePass section of the code was not present on external researchers’ reports, so we know that it is a later addition," Trend Micro told BleepingComputer.
"It is only apparent though that after gathering these intel (wallets and password configuration) is that it will send it to its C2 should they exist."
"One angle that we are looking into though is the likelihood of receiving back another set of codes/commands which would serve as remote functions in order to proceed with further functions (since it has the capability to work akin to a backdoor)."
Better protection
The new version of ViperSoftX employs several anti-detection, anti-analysis, and stealth-boosting features, starting from now using DLL sideloading to execute on the target system in the context of a trusted process, avoiding raising any alarms.
Upon arrival, the malware also checks for specific virtualization and monitoring tools like VMWare or Process Monitor and antivirus products like Windows Defender and ESET before it proceeds with the infection routine.
What's most interesting is the malware's use of "byte mapping" to encrypt its code, remapping the arrangement of shellcode bytes to make decryption and analysis without having the correct map a lot more complicated and time-consuming.
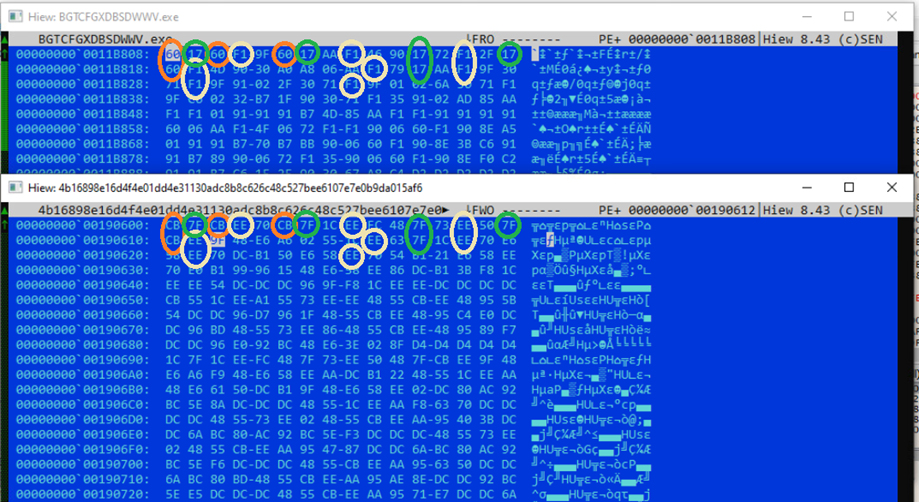
Different mapping on two executable carriers (Trend Micro)
"We have also found that each sideloader DLL has its own pair of executable and byte map, and a decryption attempt returns an incorrectly rearranged shellcode if used with another ViperSoftX-related executable," explains Trend Micro in the reported
"This ensures that the shellcode will not be decrypted without the correct DLL since the latter contains the correct byte map."
Finally, ViperSoftX features a new communication blocker on web browsers, making C2 infrastructure analysis and malicious traffic detection harder.




Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.