At least 34 distinct Russian-speaking cybercrime groups using info-stealing malware like Raccoon and Redline have collectively stolen 50,350,000 account passwords from over 896,000 individual infections from January to July 2022.
The stolen credentials were for cryptocurrency wallets, Steam, Roblox, Amazon, and PayPal accounts, as well as payment card records.
According to a report from Group-IB, whose analysts have been tracking these operations globally, most victims are based in the United States, Germany, India, Brazil, and Indonesia, but the malicious operations targeted 111 countries.
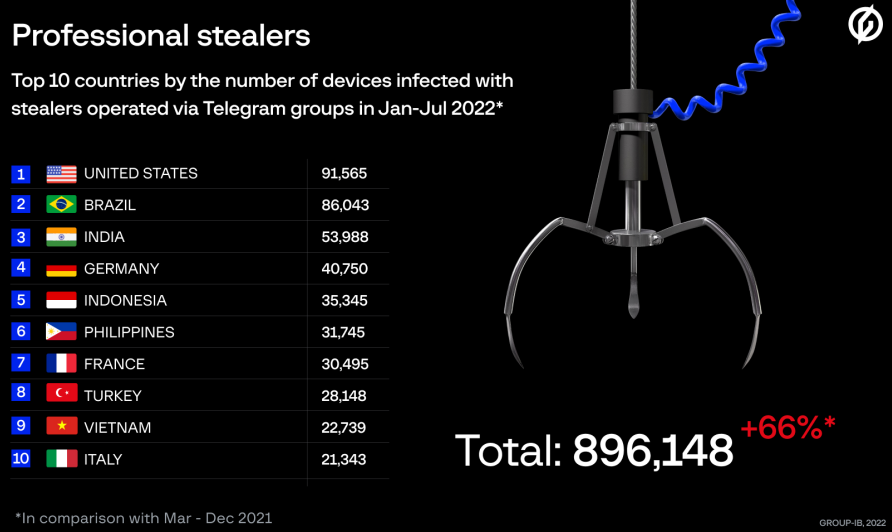
Countries with most infections between January and July 2022 (Group-IB)
Rise of info-stealers
In 2022, information-stealing malware distribution reached unprecedented levels, now involving low-skilled hackers aspiring to make a larger profit from their illegal activities.
Group-IB says the cybercriminals fueling the growth of info-stealer deployment are low-level scammers who previously worked as "victim callers" in phishing campaigns known as "Classiscam."
"The influx of a huge number of workers into the popular scam Classiscam, [...] at its peak, comprised over a thousand criminal groups and hundreds of thousands of fake websites has led to criminals competing for resources and looking for new ways to make profits," comments Group-IB.
"The popularity of schemes involving stealers can be explained by the low entry barrier. Beginners do not need to have advanced technical knowledge as the process is fully automated, and the worker's only task is to create a file with a stealer in the Telegram bot and drive traffic to it." - Group-IB
Currently, there are 34 active cybercrime groups on Telegram that operate as mass-scale information-stealing gangs, each with roughly 200 members.
23 of the groups use the Redline stealer, eight employ Raccoon, and three use their own custom malware.
SEKOIA also noted earlier this week that another info-stealer named 'Aurora' is gaining traction on underground forums and has already been adopted by seven prominent threat groups.
The increase in info-stealer activity is shown in statistics compiled by Group-IB report, who compared a 10-month period in 2021 to a seven-month period in 2022.
- Passwords stolen: 50,352,518 (up by 80%)
- Cookie files exfiltrated: 2,117,626,523 (up by 74%)
- Crypto wallets breached: 113,204 (up by 216%)
- Payment cards compromised: 103,150 (up by 81%)
.png)
Infostealer operation stats from first seven months of 2022 (Group-IB)
Group-IB also notes that in the first seven months of this year the actors focused on stealing of Steam, Epic Games, and Roblox accounts, recording a five-fold increase compared to last year.
Telegram-based operations
Telegram plays a vital role in the operation of these cybergangs, both in organizing their campaigns and maintaining a functional structure that accommodates their data-stealing activities.
These private Telegram channels offer support and technical guidance to operatives, can serve as data exfiltration points, host important announcements, act as bug-reporting portals, and also feature bots that can generate custom malware builds for clients 24/7.
The groups still abide by hierarchical rules, with the "administrators" sitting at the top of the rank, selling access to info-stealing malware to "workers" for a few hundred USD per month.
The workers are responsible for driving traffic to the malware-dropping sites, which they do by using YouTube videos, BlackSEO, SEO poisoning, laced torrent files, or malicious social media posts.
Users can minimize the chances of info-stealer infection by avoiding downloads from shady locations, checking all downloaded executables with an antivirus solution before opening, and keeping their system up to date.
- Karlston
-

 1
1




Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.