The Pakistan-based advanced persistent threat (APT) actor known as Transparent Tribe used a two-factor authentication (2FA) tool used by Indian government agencies as a ruse to deliver a new Linux backdoor called Poseidon.
"Poseidon is a second-stage payload malware associated with Transparent Tribe," Uptycs security researcher Tejaswini Sandapolla said in a technical report published this week.
"It is a general-purpose backdoor that provides attackers with a wide range of capabilities to hijack an infected host. Its functionalities include logging keystrokes, taking screen captures, uploading and downloading files, and remotely administering the system in various ways."
Transparent Tribe is also tracked as APT36, Operation C-Major, PROJECTM, and Mythic Leopard, and has a track record of targeting Indian government organizations, military personnel, defense contractors, and educational entities.
It has also repeatedly leveraged trojanized versions of Kavach, the Indian government-mandated 2FA software, to deploy a variety of malware, such as CrimsonRAT and LimePad to harvest valuable information.
Another phishing campaign detected late last year took advantage of weaponized attachments to download malware designed to exfiltrate
database files created by the Kavach app.
The latest set of attacks entail the use of a backdoored version of Kavach to target Linux users working for Indian government agencies, indicating attempts made by the threat actor to expand its attack spectrum beyond Windows and Android ecosystems.
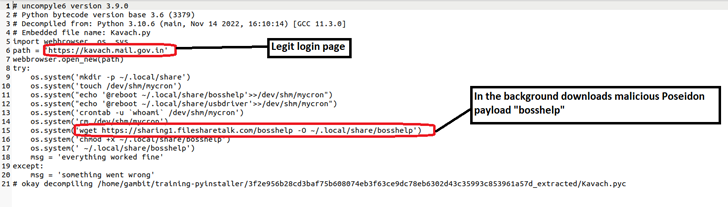
"When a user interacts with the malicious version of Kavach, the genuine login page is displayed to distract them," Sandapolla explained. "Meanwhile, the payload is downloaded in the background, compromising the user's system."
The starting point of the infections is an ELF malware sample, a compiled Python executable that's engineered to retrieve the second-stage Poseidon payload from a remote server.
The cybersecurity firm noted that the fake Kavach apps are primarily distributed through rogue websites that are disguised as legitimate Indian government sites. This includes www.ksboard[.]in and www.rodra[.]in.
With social engineering being the primary attack vector used by Transparent Tribe, users working within the Indian government are advised to double-check URLs received in emails before opening them.
"Repercussions of this APT36 attack could be significant, leading to loss of sensitive information, compromised systems, financial losses, and reputational damage," Sandapolla said.




Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.