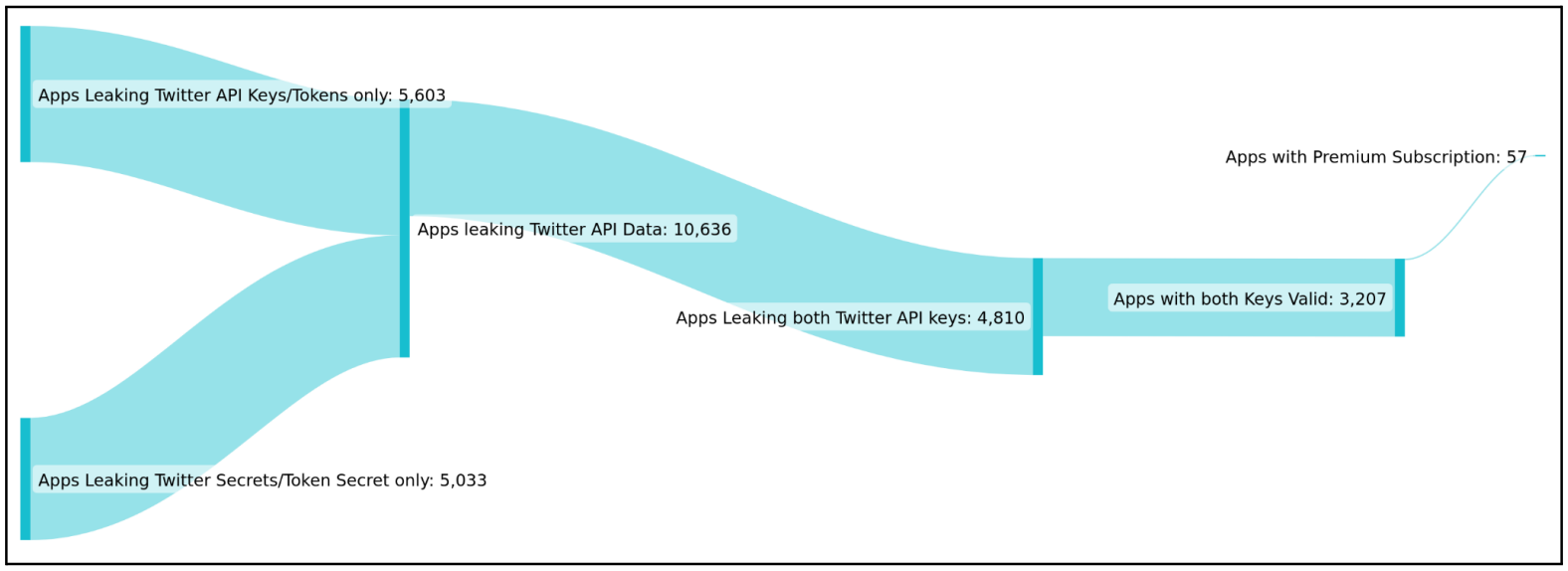
Cybersecurity researchers have uncovered a set of 3,207 mobile apps that are exposing Twitter API keys to the public, potentially enabling a threat actor to take over users' Twitter accounts that are associated with the app.
The discovery belongs to cybersecurity firm CloudSEK, which scrutinized large app sets for potential data leaks and found 3,207 leaking a valid Consumer Key and Consumer Secret for the Twitter API.
When integrating mobile apps with Twitter, developers will be given special authentication keys, or tokens, that allow their mobile apps to interact with the Twitter API. When a user associates their Twitter account with this mobile app, the keys also will enable the app to act on behalf of the user, such as logging them in via Twitter, creating tweets, sending DMs, etc.
As having access to these authentication keys could allow anyone to perform actions as associated Twitter users, it is never recommended to store keys directly in a mobile app where threat actors can find them.
Building a Twitter army
CloudSEK explains that the leak of API keys is commonly the result of mistakes by app developers who embed their authentication keys in the Twitter API but forget to remove them when the mobile is released.
In these cases, the credentials are stored within mobile applications at the following locations:
- Read someone’s direct messages
- Perform retweets and likes
- Create or delete tweets
- Remove or add new followers
- Access account settings
- Change display picture
One of the most prominent scenarios of abuse of this access, according to CloudSEK, would be for a threat actor to use these exposed tokens to create a Twitter army of verified (trustworthy) accounts with large numbers of followers to promote fake news, malware campaigns, cryptocurrency scams, etc.
Bad practices
CloudSEK explains that the leak of API keys is commonly the result of mistakes by app developers who embed their authentication keys in the Twitter API, but forget to remove them when the mobile is released.
In these cases, the credentials are stored within mobile applications at the following locations:
- resources/res/values/strings.xml
- source/resources/res/values-es-rAR/strings.xml
- source/resources/res/values-es-rCO/strings.xml
- source/sources/com/app-name/BuildConfig.java
CloudSEK recommends developers use API key rotation to protect authentication keys, which would invalidate the exposed keys after a few months.
Who is impacted?
CloudSEK shared a list of impacted applications with BleepingComputer, with apps between 50,000 and 5,000,000 downloads, including city transportation companions, radio tuners, book readers, event loggers, newspapers, e-banking apps, cycling GPS apps, and more.
Most applications publicly exposing their API keys haven't even acknowledged receiving CloudSEK's notices after a month since the cybersecurity firm alerted them, and most haven't addressed the issues.
As such, BleepingComputer will not disclose the list of apps as they are still vulnerable to exploitation and Twitter account takeover.
One notable exception was Ford Motors, which responded and deployed a fix on the 'Ford Events' app that was also leaking Twitter API keys.
Over 3,200 apps leak Twitter API keys, some allowing account hijacks
- aum
-

 1
1



3175x175(CURRENT).thumb.jpg.b05acc060982b36f5891ba728e6d953c.jpg)
Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.