Microsoft on Monday revealed new malware deployed by the hacking group behind the SolarWinds supply chain attack last December to deliver additional payloads and steal sensitive information from Active Directory Federation Services (AD FS) servers.
The tech giant's Threat Intelligence Center (MSTIC) codenamed the "passive and highly targeted backdoor" FoggyWeb, making it the threat actor tracked as Nobelium's latest tool in a long list of cyber weaponry such as Sunburst, Sunspot, Raindrop, Teardrop, GoldMax, GoldFinder, Sibot, Flipflop, NativeZone, EnvyScout, BoomBox, and VaporRage.
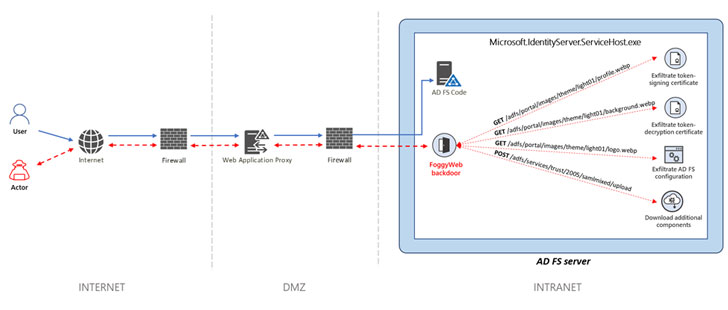
"Once Nobelium obtains credentials and successfully compromises a server, the actor relies on that access to maintain persistence and deepen its infiltration using sophisticated malware and tools," MSTIC researchers said. "Nobelium uses FoggyWeb to remotely exfiltrate the configuration database of compromised AD FS servers, decrypted token-signing certificate, and token-decryption certificate, as well as to download and execute additional components."
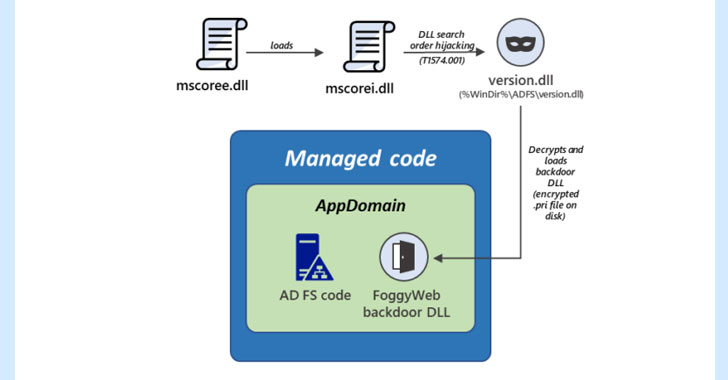
Microsoft said it observed FoggyWeb in the wild as early as April 2021, describing the implant as a "malicious memory-resident DLL."
Nobelium is the moniker assigned by the company to the nation-state hacking group widely known as APT29, The Dukes, or Cozy Bear — an advanced persistent threat that has been attributed to Russia's Foreign Intelligence Service (SVR) — and believed to have been behind the wide-ranging attack targeting SolarWinds that came to light in December 2020. The adversary behind this campaign is also being monitored under a variety of codenames like UNC2452 (FireEye), SolarStorm (Unit 42), StellarParticle (CrowdStrike), Dark Halo (Volexity), and Iron Ritual (Secureworks).
FoggyWeb, installed using a loader by exploiting a technique called DLL search order hijacking, is capable of transmitting sensitive information from a compromised AD FS server as well as receive and execute additional malicious payloads retrieved from a remote attacker-controlled server. It's also engineered to monitor all incoming HTTP GET and POST requests sent to the server from the intranet (or internet) and intercept HTTP requests that are of interest to the actor.
"Protecting AD FS servers is key to mitigating Nobelium attacks," the researchers said. "Detecting and blocking malware, attacker activity, and other malicious artifacts on AD FS servers can break critical steps in known Nobelium attack chains. Customers should review their AD FS Server configuration and implement changes to secure these systems from attacks."
- Karlston
-

 1
1



Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.