A set of memory corruption flaws have been discovered in the ncurses (short for new curses) programming library that could be exploited by threat actors to run malicious code on vulnerable Linux and macOS systems.
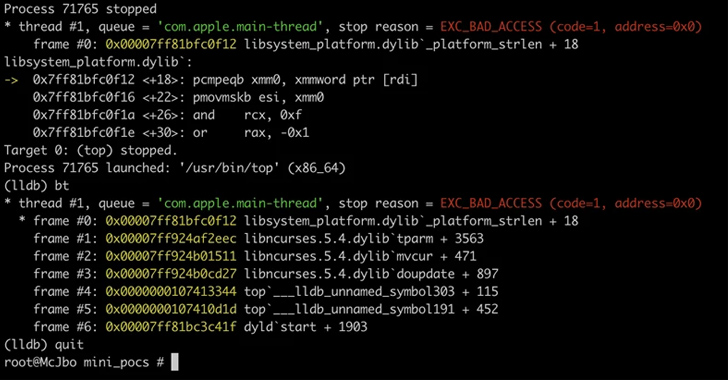
"Using environment variable poisoning, attackers could chain these vulnerabilities to elevate privileges and run code in the targeted program's context or perform other malicious actions," Microsoft Threat Intelligence researchers Jonathan Bar Or, Emanuele Cozzi, and Michael Pearse said in a technical report published today.
The vulnerabilities, collectively tracked as CVE-2023-29491 (CVSS score of 7.8), have been addressed as of April 2023. Microsoft said it also worked with Apple on addressing the macOS-specific issues related to these flaws.
Environment variables are user-defined values that can be used by multiple programs on a system and can affect the manner in which they behave on the system. Manipulating the variables can cause applications to perform otherwise unauthorized operations.
Microsoft's code auditing and fuzzing found that the ncurses library searches for several environment variables, including TERMINFO, which could be poisoned and combined with the identified flaws to achieve privilege escalation. Terminfo is a database that enables programs to use display terminals in a device-independent manner.
The flaws encompass a stack information leak, a parameterized string type confusion, an off-by-one error, a heap out-of-bounds during terminfo database file parsing, and a denial-of-service with canceled strings.
"The discovered vulnerabilities could have been exploited by attackers to elevate privileges and run code within a targeted program's context," the researchers said. "Nonetheless, gaining control of a program through exploiting memory corruption vulnerabilities requires a multi-stage attack."
"The vulnerabilities may have needed to be chained together for an attacker to elevate privileges, such as exploiting the stack information leak to gain arbitrary read primitives along with exploiting the heap overflow to obtain a write primitive."
- Adenman
-

 1
1



Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.