Microsoft on Monday announced the seizure of 42 domains used by a China-based cyber espionage group that set its sights on organizations in the U.S. and 28 other countries pursuant to a legal warrant issued by a federal court in the U.S. state of Virginia.
The Redmond company attributed the malicious activities to a group it pursues as Nickel, and by the wider cybersecurity industry under the monikers APT15, Bronze Palace, Ke3Chang, Mirage, Playful Dragon, and Vixen Panda. The advanced persistent threat (APT) actor is believed to have been active since at least 2012.
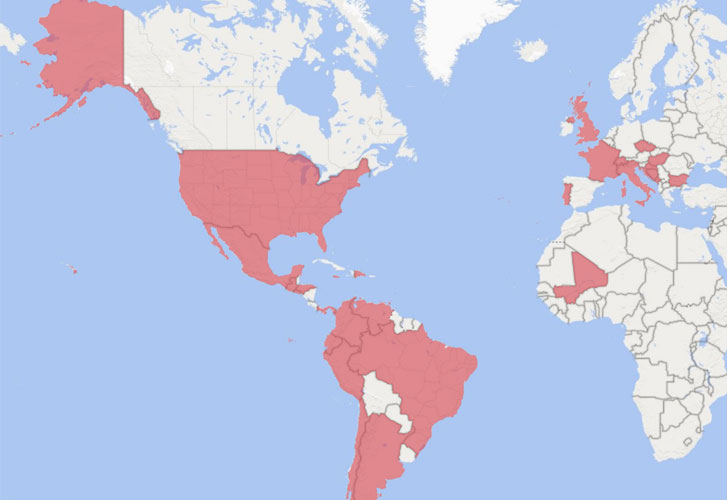
"Nickel has targeted organizations in both the private and public sectors, including diplomatic organizations and ministries of foreign affairs in North America, Central America, South America, the Caribbean, Europe and Africa," Microsoft's Corporate Vice President for Customer Security and Trust, Tom Burt, said. "There is often a correlation between Nickel's targets and China's geopolitical interests."
The rogue infrastructure enabled the hacking crew to maintain long-term access to the compromised machines and execute attacks for intelligence gathering purposes targeting unnamed government agencies, think tanks, and human rights organizations as part of a digital espionage campaign dating back to September 2019.
Microsoft painted the cyber assaults as "highly sophisticated" that used a multitude of techniques, including breaching remote access services and exploiting vulnerabilities in unpatched VPN appliances as well as Exchange Server and SharePoint systems to "insert hard-to-detect malware that facilitates intrusion, surveillance and data theft."
Upon gaining an initial foothold, Nickel has been found deploying credential dumping tools and stealers such as Mimikatz and WDigest to hack into victim accounts, followed by delivering custom malware that allowed the actor to maintain persistence on victim networks over extended periods of time and conduct regularly scheduled exfiltration of files, execute arbitrary shellcode, and collect emails from Microsoft 365 accounts using compromised credentials.
The multiple backdoor families used for command and control are being tracked as Neoichor, Leeson, NumbIdea, NullItch, and Rokum.
The latest wave of attacks adds to an extensive list of surveillanceware campaigns mounted by the APT15 group in recent years. In July 2020, mobile security firm Lookout disclosed four trojanized legitimate apps — named SilkBean, DoubleAgent, CarbonSteal, and GoldenEagle — that targeted the Uyghur ethnic minority and the Tibetan community with the goal of gathering and transmitting personal user data to adversary-operated command-and-control servers.
"As China's influence around the world continues to grow and the nation establishes bilateral relations with more countries and extends partnerships in support of China's Belt and Road Initiative, we assess that China-based threat actors will continue to target customers in government, diplomatic, and NGO sectors to gain new insights, likely in pursuit of economic espionage or traditional intelligence collection objectives," Microsoft said.
Also: Microsoft Seizes 42 Domains Used by Chinese Hacking Group Nickel.
- Mutton
-

 1
1



Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.