Microsoft has shed light on four different ransomware families – KeRanger, FileCoder, MacRansom, and EvilQuest – that are known to impact Apple macOS systems.
"While these malware families are old, they exemplify the range of capabilities and malicious behavior possible on the platform," the tech giant's Security Threat Intelligence team said in a Thursday report.
The initial vector for these ransomware families involves what the Windows maker calls "user-assisted methods," wherein the victim downloads and installs trojanized applications.
Alternatively, it can also arrive as a second-stage payload that's dropped by an already existing malware on the infected host or as part of a supply chain attack.
Irrespective of the modus operandi employed, the attacks proceed along similar lines, with the threat actors relying on legitimate operating system features and exploiting vulnerabilities to break into the systems and encrypt files of interest.
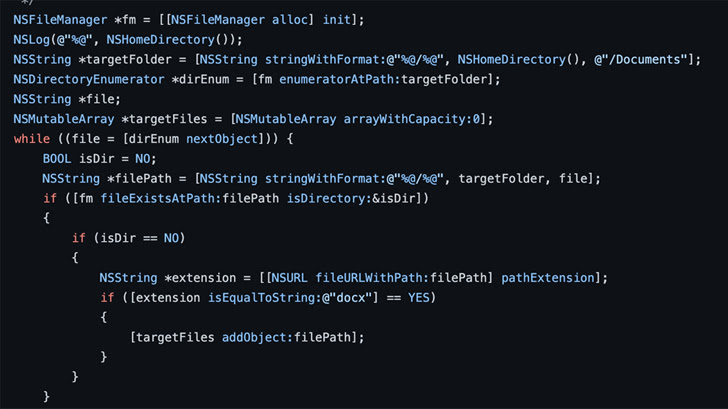
This includes the use of the Unix find utility as well as library functions like opendir, readdir, and closedir to enumerate files. Another method touched on by Microsoft, but not adopted by the ransomware strains, entails the NSFileManager Objective-C interface.
KeRanger, MacRansom, and EvilQuest have also been observed to utilize a combination of hardware- and software-based checks to determine if the malware is running in a virtual environment in an attempt to resist analysis and debugging attempts.
KeRanger, notably, employs a technique known as delayed execution to escape detection. It achieves this by sleeping for three days upon its launch before kick-starting its malicious functions.
Persistence, which is essential to ensuring that the malware is run even after a system restart, is established by means of launch agents and kernel queues, Microsoft pointed out.
While FileCoder uses the ZIP utility to encrypt files, KeRanger uses AES encryption in cipher block chaining (CBC) mode to achieve its goals. Both MacRansom and EvilQuest, on the other hand, leverage a symmetric encryption algorithm.
EvilQuest, which was first exposed in July 2020, further goes beyond typical ransomware to incorporate other trojan-like features, such as keylogging, compromising Mach-O files by injecting arbitrary code, and disabling security software.
It also packs in capabilities to execute any file directly from memory, effectively leaving no trace of the payload on disk.
"Ransomware continues to be one of the most prevalent and impactful threats affecting organizations, with attackers constantly evolving their techniques and expanding their tradecraft to cast a wider net of potential targets," Microsoft said.




Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.