Microsoft has added command-and-control (C2) traffic detection capabilities to its Microsoft Defender for Endpoint (MDE) enterprise endpoint security platform.
Available in public preview at the moment, this new MDE feature will allow security admins to detect malware attempting to communicate with attacker-controlled servers at the network layer.
The C2 connections are detected by the Defender for Endpoint's Network Protection (NP) agent by mapping the outbound connection's IP address, port, hostname, and other values with data from Microsoft Cloud.
If the connection is evaluated as malicious by Microsoft's cloud-powered AI and scoring engines, MDE will automatically block the connection and roll back the malware binaries to a previous clean state.
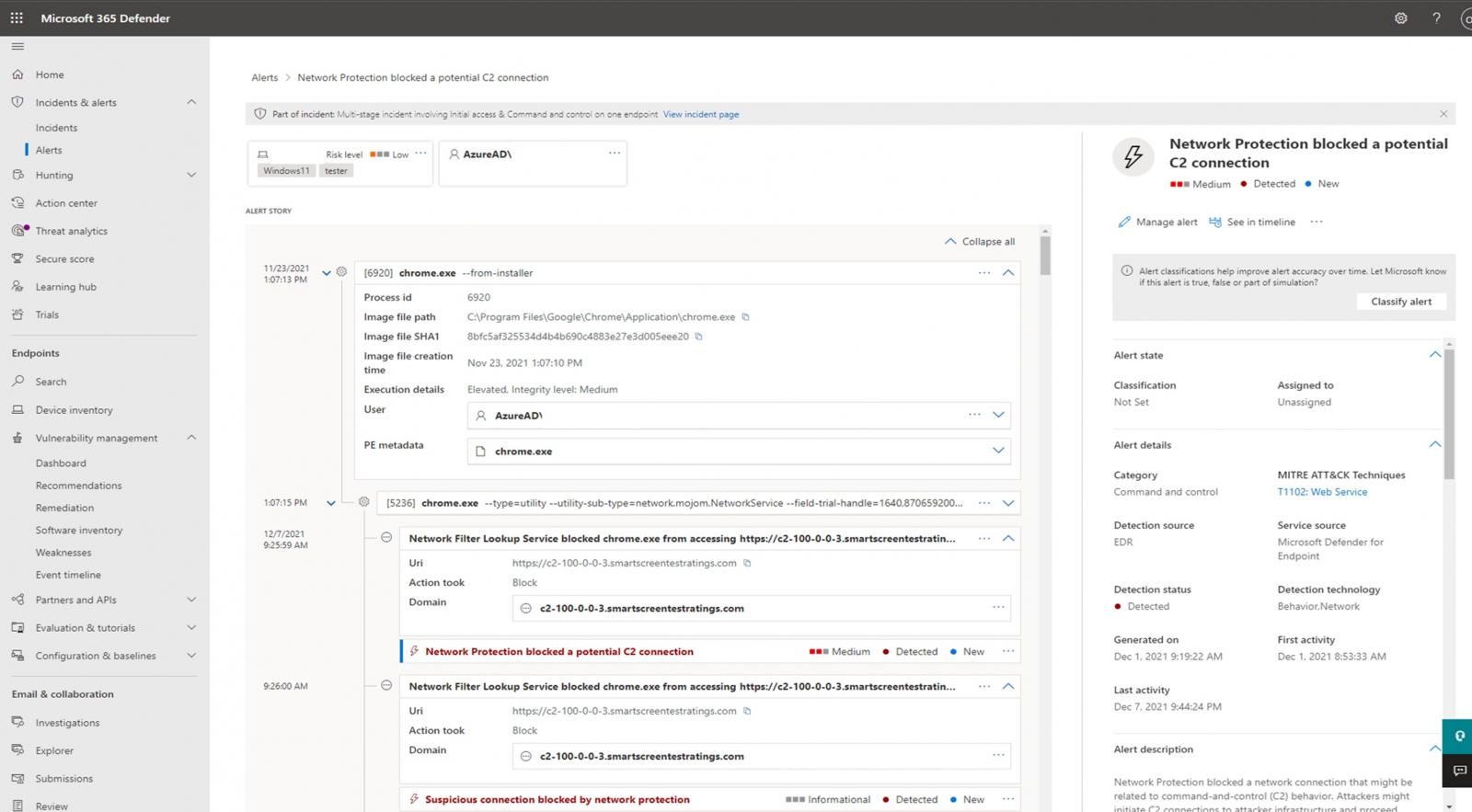
After the malicious connection is detected, a "Network Protection blocked a potential C2 connection" alert will be added to the Microsoft 365 Defender portal, providing SecOps team members with details, including the severity level and the impacted assets, and the activity timespan.
More info, such as the attack flow and a full timeline, is available after opening the C2 connection alert, as shown in the screenshot below.
"SecOps teams need precise alerts that can accurately define areas of compromise and previous connections to known malicious IPs," MDE senior program manager Oludele Ogunrinde said.
"With the new capabilities in Microsoft Defender for Endpoint, SecOps teams can detect network C2 attacks earlier in the attack chain, minimize the spread by rapidly blocking any further attack propagation, and reduce the time it takes to mitigate by easily removing malicious binaries."
The prerequisites include Microsoft Defender Antivirus with active real-time protection and cloud-delivered protection, MDE in active mode, network protection in block mode, and engine version 1.1.17300.4 or later installed.
It works with both consumer (Windows 10 version 1709 or later) and server (Windows Server 1803, Windows Server 2019 or later) platforms.
The new capability will be gradually and automatically applied in environments where Network Protection (NP) is enabled if you've already signed up for the public preview.
Last month, Microsoft also said tamper protection would soon be turned on by default in Microsoft Defender for Endpoint for better defense against ransomware attacks.
- Karlston
-

 1
1




Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.