The number of malware infections targeting Linux devices rose by 35% in 2021, most commonly to recruit IoT devices for DDoS (distributed denial of service) attacks.
IoTs are typically under-powered "smart" devices running various Linux distributions and are limited to specific functionality. However, when their resources are combined into large groups, they can deliver massive DDoS attacks to even well-protected infrastructure.
Besides DDoS, Linux IoT devices are recruited to mine cryptocurrency, facilitate spam mail campaigns, serve as relays, act as command and control servers, or even act as entry points into corporate networks.
A Crowdstrike report looking into the attack data from 2021 summarizes the following:
- In 2021, there was a 35% rise in malware targeting Linux systems compared to 2020.
- XorDDoS, Mirai, and Mozi were the most prevalent families, accounting for 22% of all Linux-targeting malware attacks observed in 2021.
- Mozi, in particular, had explosive growth in its activity, with ten times more samples circulating in the wild the year that passed compared to the previous one.
- XorDDoS also had a notable year-over-year increase of 123%.
Malware overview
XorDDoS is a versatile Linux trojan that works in multiple Linux system architectures, from ARM (IoT) to x64 (servers). It uses XOR encryption for C2 communications, hence the name.
When attacking IoT devices, XorDDoS brute-forces vulnerable devices via SSH. On Linux machines, it uses port 2375 to gain password-less root access to the host.
A notable case of the malware's distribution was shown in 2021 after a Chinese threat actor known as "Winnti" was observed deploying it with other derivative botnets.
Mozi is a P2P botnet relying on the distributed hash table (DHT) lookup system to hide suspicious C2 communications from network traffic monitoring solutions.
The particular botnet has been around for a while, continually adding more vulnerabilities and expanding its targeting scope.
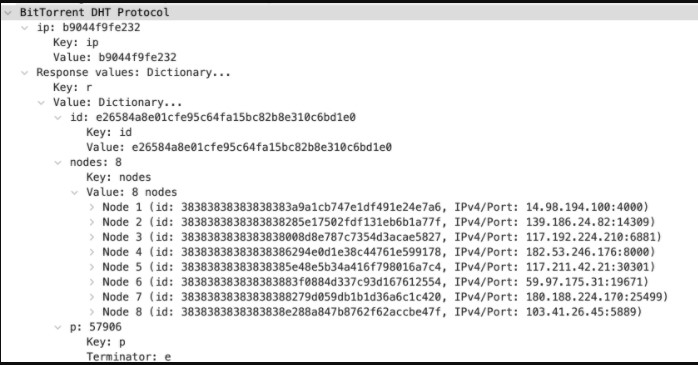
DHT system implemented in Mozi
Source: Crowdstrike
Mirai is a notorious botnet that spawned numerous forks due to its publicly available source code that continues to plague the IoT world.
The various derivatives implement different C2 communication protocols, but they all typically abuse weak credentials to brute-force into devices.
We covered several notable Mirai variants in 2021, like "Dark Mirai," which focuses on home routers, and "Moobot," which targets cameras.
"Some of the most prevalent variants tracked by CrowdStrike researchers involve Sora, IZIH9 and Rekai," says CrowdStrike researcher Mihai Maganu in the report. "Compared to 2020, the numbers of identified samples for all three variants have increased by 33%, 39% and 83% respectively in 2021."
A trend that continues into 2022
The Crowstrike findings aren't surprising as they confirm an ongoing trend that emerged in previous years.
For example, an Intezer report analyzing 2020 stats found that Linux malware families increased by 40% in 2020 compared to the previous year.
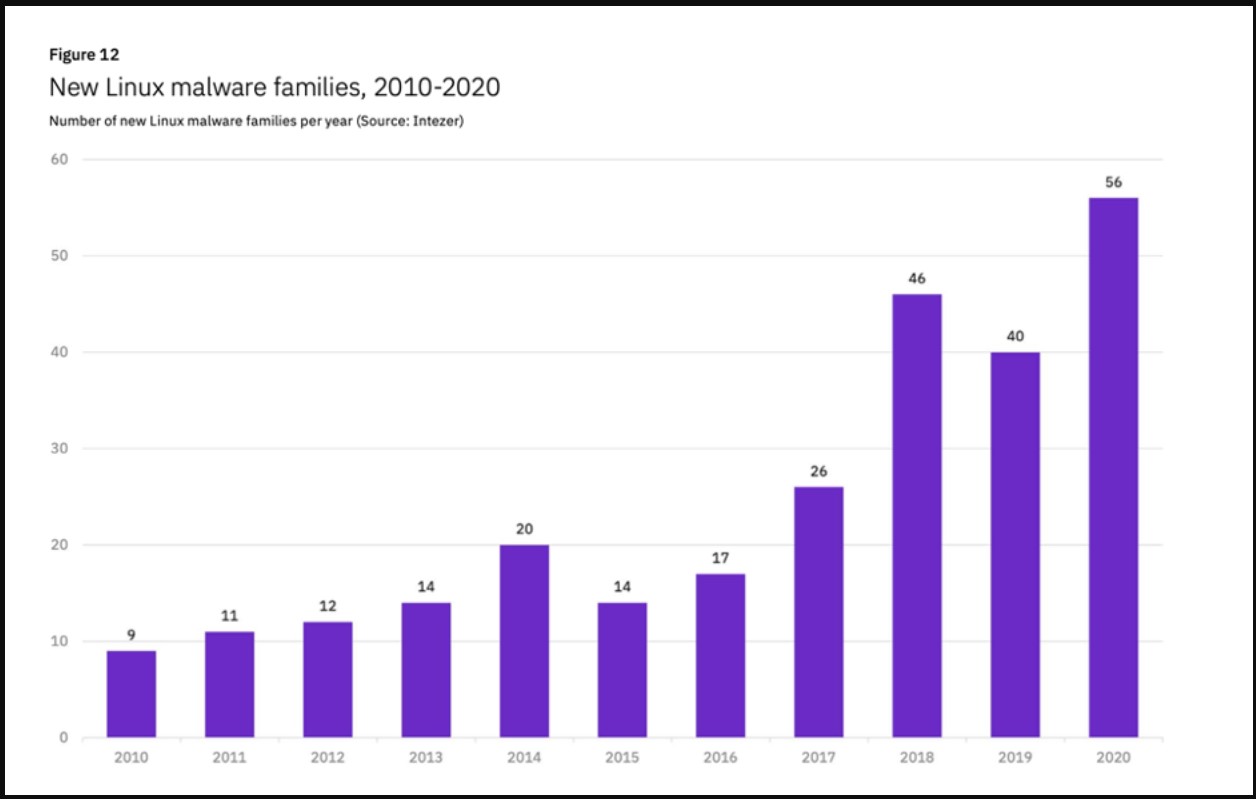
Linux malware families recorded in recent years
Source: Intezer
In the first six months of 2020, a steep rise of 500% in Golang malware was recorded, showing that malware authors were looking for ways to make their code run on multiple platforms.
This programming, and by extension, targeting trend, has already been confirmed in early 2022 cases and is likely to continue unabated.
- DKT27 and Karlston
-

 2
2



Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.