A novel Linux Kernel cross-cache attack named SLUBStick has a 99% success in converting a limited heap vulnerability into an arbitrary memory read-and-write capability, letting the researchers elevate privileges or escape containers.
The discovery comes from a team of researchers from the Graz University of Technology who demonstrated the attack on Linux kernel versions 5.9 and 6.2 (latest) using nine existing CVEs in both 32-bit and 64-bit systems, indicating high versatility.
Additionally, the attack worked with all modern kernel defenses like Supervisor Mode Execution Prevention (SMEP), Supervisor Mode Access Prevention (SMAP), and Kernel Address Space Layout Randomization (KASLR) active.
SLUBStick will be presented in detail at the upcoming Usenix Security Symposium conference later this month. The researchers will showcase privilege escalation and container escape in the latest Linux with state-of-the-art defenses enabled.
In the meantime, the published technical paper contains all the details about the attack and the potential exploitation scenarios.
SLUBStick details
One way the Linux kernel manages memory efficiently and securely is by allocating and de-allocating memory chunks, called "slabs," for different types of data structures.
Flaws in this memory management process may allow attackers to corrupt or manipulate data structures, called cross-cache attacks. However, these are effective roughly 40% of the time and typically lead to system crashes sooner or later.
SLUBStick exploits a heap vulnerability, such as a double-free, user-after-free, or out-of-bounds write, to manipulate the memory allocation process.
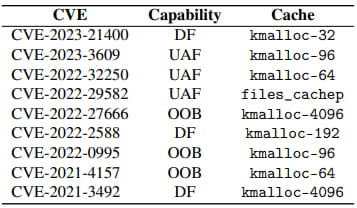
CVEs successfully used in the researchers' experiments
Source: stefangast.eu
Next, it uses a timing side channel to determine the exact moment of memory chunk allocation/deallocation, allowing the attacker to predict and control memory reuse.
Using this timing information raises the success of the cross-change exploitation to 99%, making SLUBStick very practical.
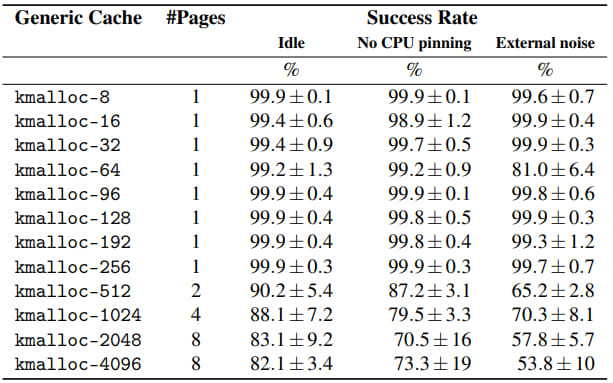
Measured success rates
Source: stefangast.eu
The conversion of the heap flaw into arbitrary memory read-and-write primitive is done in three steps:
- Free specific memory chunks and wait for the kernel to reuse them.
- Reallocate these chunks in a controlled manner, ensuring they get repurposed for critical data structures like page tables.
- Once reclaimed, the attacker overwrites the page table entries, getting the ability to read and write any memory location.
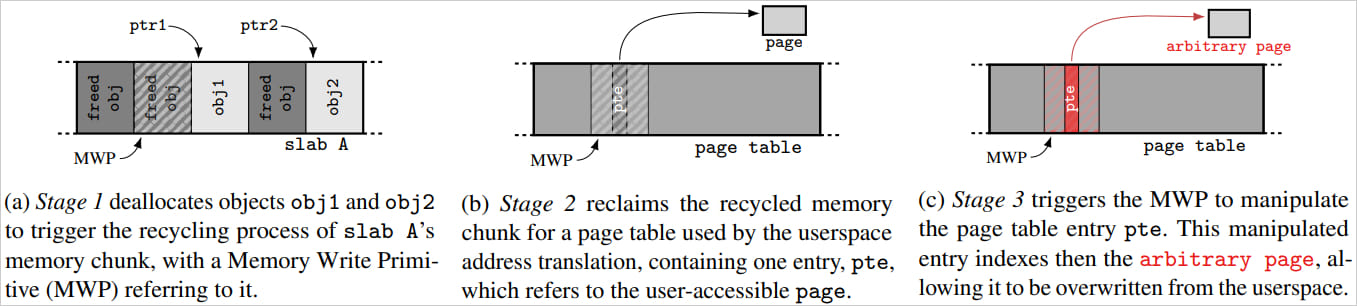
SLUBStick overview
Source: stefangast.eu
Real-world impact
As with most attacks involving a side channel, SLUBStick requires local access on the target machine with code execution capabilities. Furthermore, the attack requires the presence of a heap vulnerability in the Linux kernel, which will then be used to gain read and write access to the memory.
While this may make the attack appear impractical, it does introduce some benefits to attackers.
Even for attackers with code execution capabilities, SLUBStick provides the ability to achieve privilege escalation, bypass kernel defenses, perform container escapes, or use it as part of a complex attack chain.
Privilege escalation can be used to elevate privileges to root, allowing unlimited operations, while container escape can be used to break from sandboxed environments and access the host system.
Additionally, in the post-exploitation phase, SLUBStick could modify kernel structures or hooks to maintain persistence, making malware harder for defenders to detect.
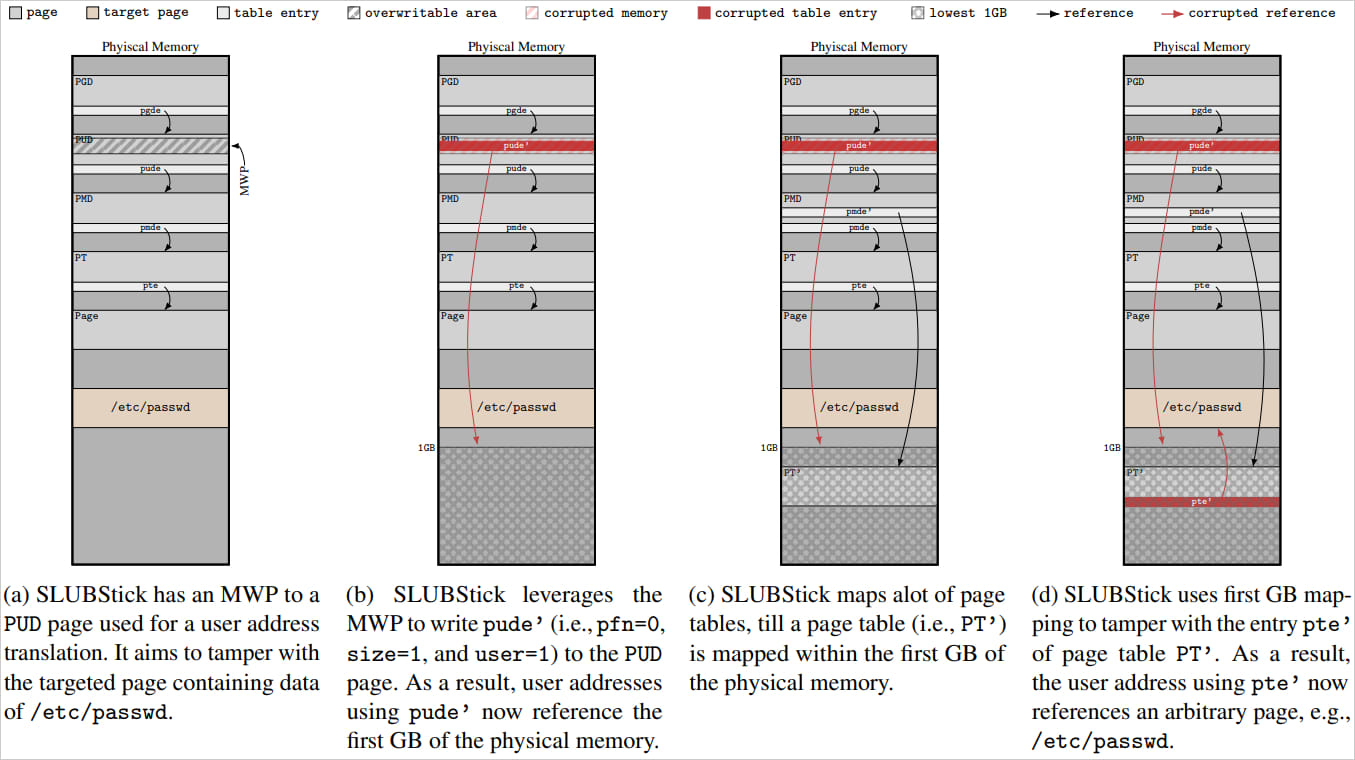
Tampering with '/etc/passwd' data
Source: stefangast.eu
Those who want to dive deeper into SLUBStick and experiment with the exploits used by the Graz University researchers can find them in the researcher's GitHub repository.




Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.