Researchers on Monday took the wraps off a newly discovered Linux and Windows re-implementation of Cobalt Strike Beacon that's actively set its sights on government, telecommunications, information technology, and financial institutions in the wild.
The as-yet undetected version of the penetration testing tool — codenamed "Vermilion Strike" — marks one of the rare Linux ports, which has been traditionally a Windows-based red team tool heavily repurposed by adversaries to mount an array of targeted attacks. Cobalt Strike bills itself as a "threat emulation software," with Beacon being the payload engineered to model an advanced actor and duplicate their post-exploitation actions.
"The stealthy sample uses Cobalt Strike's command-and-control (C2) protocol when communicating to the C2 server and has remote access capabilities such as uploading files, running shell commands and writing to files," Intezer researchers said in a report published today and shared with The Hacker News.
The Israeli cybersecurity company's findings come from an artifact uploaded to VirusTotal on August 10 from Malaysia. As of writing, only two anti-malware engines flag the file as malicious.
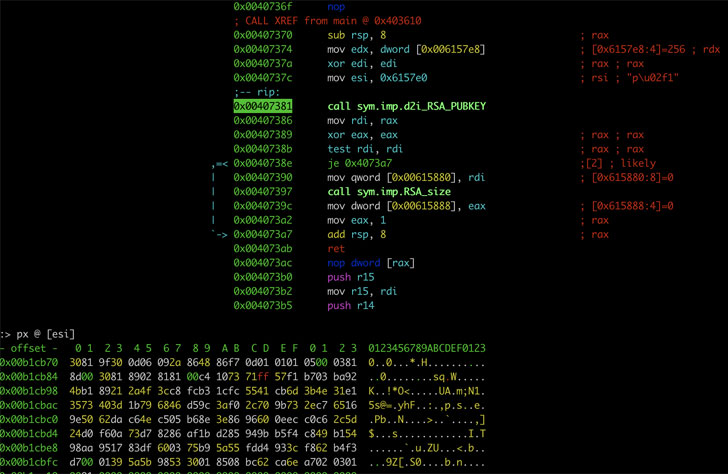
Once installed, the malware runs itself in the background and decrypt the configuration necessary for the beacon to function, before fingerprinting the compromised Linux machine and establishing communications with a remote server over DNS or HTTP to retrieve base64-encoded and AES-encrypted instructions that allow it run arbitrary commands, write to files, and upload files back to the server.
Interestingly, additional samples identified during the course of the investigation have shed light on the Windows variant of the malware, sharing overlaps in the functionality and the C2 domains used to remotely commandeer the hosts. Intezer also called out the espionage campaign's limited scope, noting the malware's use in specific attacks as opposed to large-scale intrusions, while also attributing it to a "skilled threat actor" owing to the fact that Vermilion Strike has not been observed in other attacks to date.
"Vermilion Strike and other Linux threats remain a constant threat. The predominance of Linux servers in the cloud and its continued rise invites APTs to modify their toolsets in order to navigate the existing environment," the researchers said.
- Karlston
-

 1
1


Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.