HP has released BIOS updates today to fix two high-severity vulnerabilities affecting a wide range of PC and notebook products, which allow code to run with Kernel privileges.
Kernel-level privileges are the highest rights in Windows, allowing threat actors to execute any command at the Kernel level, including manipulating drivers and accessing the BIOS.
The flaws are tracked as CVE-2021-3808 and CVE-2021-3809, and both have a CVSS 3.1 base score of 8.8, giving them a high severity rating. At this time, HP has provided no technical details about these flaws.
“Potential security vulnerabilities have been identified in the BIOS (UEFI Firmware) for certain HP PC products, which might allow arbitrary code execution. HP is releasing firmware updates to mitigate these potential vulnerabilities,” reads the short advisory.
The list of affected products includes business notebooks like Zbook Studio, ZHAN Pro, EliteBook, ProBook, and Elite Dragonfly, business desktop PCs like the EliteDesk and ProDesk, retail PoS computers like the Engage, workstations like the Z1 and Z2, and thin client PCs.
For a complete list of all the affected models and the corresponding SoftPaqs to use in each case, check the security advisory page and look for your device. Note that not all of the listed products have received a fixing patch yet.
Researcher discloses more
Nicholas Starke, the researcher who discovered these flaws in November 2021, and reported them to HP, explains the problem in greater detail in a separate blog post.
“This vulnerability could allow an attacker executing with kernel-level privileges (CPL == 0) to escalate privileges to System Management Mode (SMM). Executing in SMM gives an attacker full privileges over the host to further carry out attacks.” explains a report by Starke.
The problem appears to be that an SMI handler can be triggered from the OS environment, for example, through the Windows kernel driver.
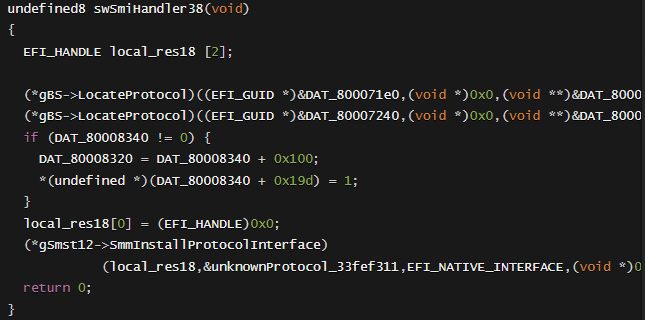
The vulnerable SMI handler (StarkeBlog)
An attacker needs to locate the memory address of the “LocateProtocol” function and overwrite it with malicious code. Finally, the attacker can trigger code execution by instructing the SMI handler to execute.
It's important to underline that to exploit the vulnerability, an attacker would need to have root/SYSTEM level privileges on the target system, and execute code in System Management Mode (SMM).
The ultimate goal of such an attack would be to overwrite the UEFI Implementation (BIOS) of the machine with attacker controlled BIOS images. This means an attacker could plant persistent malware that can't be removed by antivirus tools, and not even with OS reinstalls.
Finally, it's also crucial to highlight that some HP computer models have mitigations that the attacker would need to bypass in order for the exploit to work, like the HP Sure Start system for example.
The researcher explains that HP Sure Start can detect tampering of this kind and shut down the host upon the memory corruption act. Then, at first startup, a warning will be displayed to the user along with a prompt to approve the system boot.
HP’s latest fixes come only two months after the computer maker plugged 16 UEFI firmware bugs and three months after addressing a different set of BIOS flaws.
As such, if you haven’t applied the security updates yet, make sure to take a backup of your data on a separate system and do so now.
HP fixes bug letting attackers overwrite firmware in over 200 models


3175x175(CURRENT).thumb.jpg.b05acc060982b36f5891ba728e6d953c.jpg)

Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.