A threat actor claims to be selling public and private data of 400 million Twitter users scraped in 2021 using a now-fixed API vulnerability. They're asking $200,000 for an exclusive sale.
The alleged data dump is being sold by a threat actor named 'Ryushi' on the Breached hacking forum, a site commonly used to sell user data stolen in data breaches.
The threat actor claimed to have collected the data of 400+ million unique Twitter users using a vulnerability. They warned Elon Musk and Twitter that they should purchase the data before it leads to a large fine under Europe's GDPR privacy law.
"Twitter or Elon Musk if you are reading this you are already risking a GDPR fine over 5.4m breach imaging the fine of 400m users breach source," wrote Ryushi in a forum post.
"Your best option to avoid paying $276 million USD in GDPR breach fines like facebook did (due to 533m users being scraped) is to buy this data exclusively."
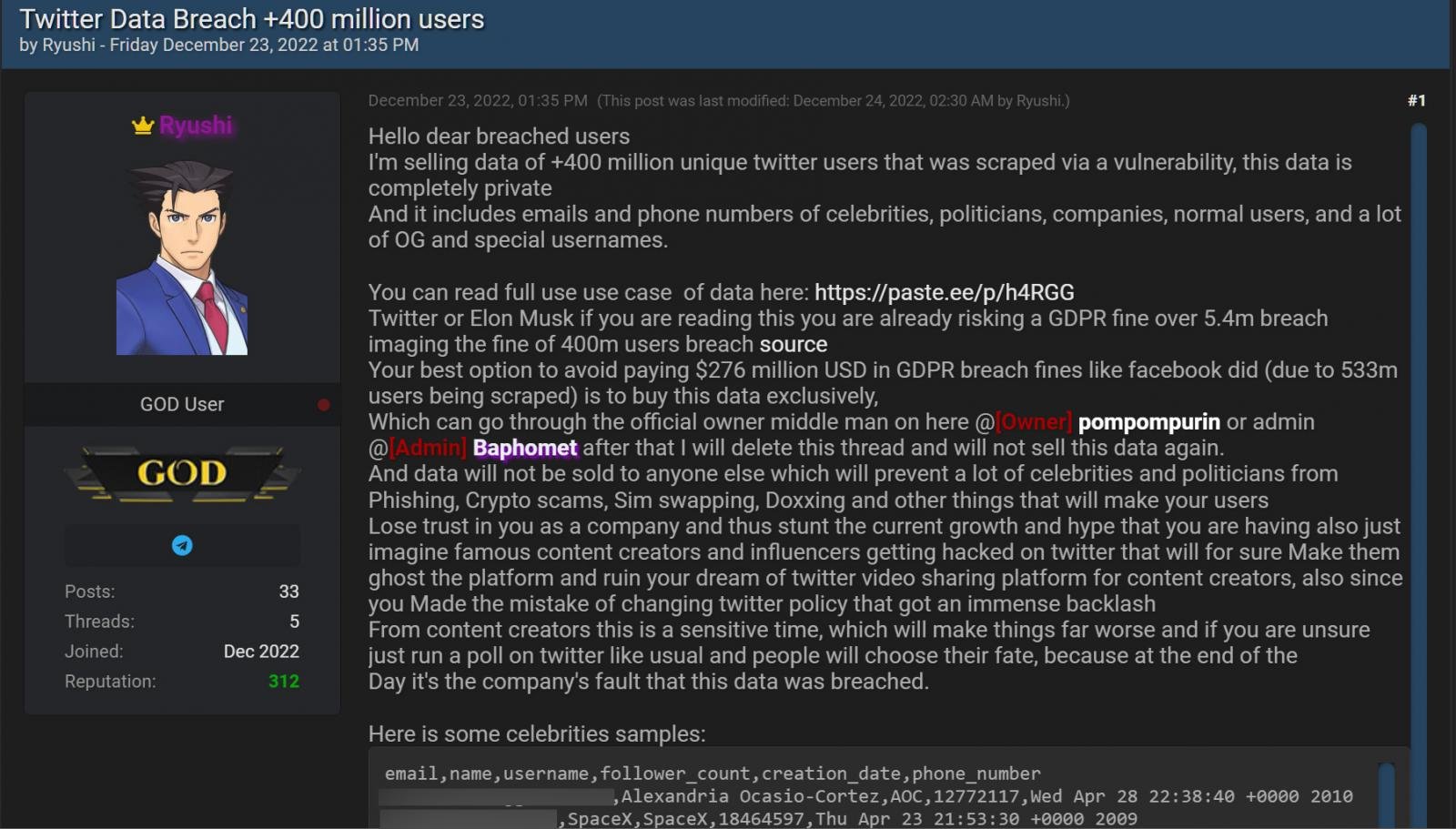
Forum post selling the data for an alleged 400 million Twitter users
Source: BleepingComputer
The threat actor also linked to a post explaining how this data could be abused by other threat actors for phishing attacks, crypto scams, and BEC attacks.
The forum post includes sample data for thirty-seven celebrities, politicians, journalists, corporations, and government agencies, including Alexandria Ocasio-Cortez, Donald Trump JR, Mark Cuba, Kevin O'Leary, and Piers Morgan. In addition, a larger sample of 1,000 Twitter user profiles was leaked later.
The user profiles contain public and private Twitter data, including users' email addresses, names, usernames, follower count, creation date, and phone numbers. Although all of the leaked profiles appear to have email addresses associated with them, many do not have phone numbers.
While almost all of this data is publicly accessible to any Twitter user, phone numbers and email addresses are private information.
The threat actor Ryushi told BleepingComputer that they are attempting to sell the Twitter data exclusively to a single person/Twitter for $200,000 and will then delete the data. If an exclusive purchase is not made, they will sell copies to multiple people for $60,000 per sale.
When asked if they contacted Twitter to ransom the data, they told BleepingComputer that they contacted Twitter and made calls but did not receive a response.
Data collected using now-fixed API vulnerability
The threat actor confirmed to BleepingComputer that they collected the private phone numbers and email addresses using an API vulnerability that Twitter fixed in January 2022 and was previously associated with a 5.4 million user data breach.
This vulnerability allowed a person to feed large lists of phone numbers and email addresses into a Twitter API and receive an associated Twitter user ID. The threat actor then used this ID with another IP to retrieve the public profile data for the users, building a Twitter user profile consisting of public and private data.
"I gained access by same exploit used for 5.4m data leak already. Spoke with the seller of it and he confirmed it was in twitter login flow", the threat actor told BleepingComputer.
"So, in the check for duplication it leaked the userID which i converted using another api to username and other info."
While Twitter fixed the vulnerability in January 2022, it has now been confirmed to have been used by multiple threat actors to scrape private information from Twitter users.
As for this new leak, BleepingComputer has only been able to confirm two of the leaked Twitter profiles as valid.
However, Alon Gal of threat intelligence company Hudson Rock has said that they independently verified that the leaked samples appear legitimate.
"Please Note:At this stage it is not possible to fully verify that there are indeed 400,000,000 users in the database," tweeted Hudson Rock.
"From an independent verification the data itself appears to be legitimate and we will follow up with any developments."
This leak of Twitter user data comes at a bad time for the social media company, as an EU privacy watchdog, the Irish Data Protection Commission (DPC), has begun an investigation into the recent publishing of the 5.4 million user records stolen in 2021 using this vulnerability.
Another threat actor claimed to have also used this vulnerability to scrape the data of an alleged 17 million users. However, this leak is still private and is not being sold.
BleepingComputer reached out to Twitter with further questions regarding the sale of this data, but a response was not immediately available.
- Karlston, aum and Asciito
-

 3
3




Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.