A cybersecurity researcher is urging users to upgrade Adobe Acrobat Reader after a fix was released yesterday for a remote code execution zero-day with a public in-the-wild proof-of-concept exploit.
The flaw is tracked as CVE-2024-41869 and is a critical use after free vulnerability that could lead to remote code execution when opening a specially crafted PDF document.
A "use after free" bug is when a program tries to access data in a memory location that has already been freed or released. This causes unexpected behavior, such as a program crashing or freezing.
However, if a threat actor is able to store malicious code in that memory location, and the program subsequently accesses it, it could be used to execute malicious code on the targeted device.
The flaw has now been fixed in the latest Acrobat Reader and Adobe Acrobat versions.
PoC exploit discovered in June
The Acrobat Reader zero-day was discovered in June through EXPMON, a sandbox-based platform created by cybersecurity researcher Haifei Li to detect advanced exploits such as zero-days or hard-to-detect (unknown) exploits.
"I created EXPMON because I noticed that there were no sandbox-based detection and analysis systems specifically focusing on detecting threats from an exploit or vulnerability perspective," Li told BleepingComputer.
"All the other systems do detection from a malware perspective. The exploit/vulnerability perspective is much needed if you want to go more advanced (or, early) detection."
"For example, if no malware is dropped or executed due to certain conditions, or if the attack does not use any malware at all, those systems would miss such threats. Exploits operate quite differently from malware, so a different approach is needed to detect them."
The zero-day was discovered after a large number of samples from a public source were submitted to EXPMON for analysis. These samples included a PDF containing a proof-of-concept exploit that caused a crash.
While the PoC exploit is a work in progress and contains no malicious payloads, it was confirmed to exploit a "user after free" bug, which could be used for remote code execution.
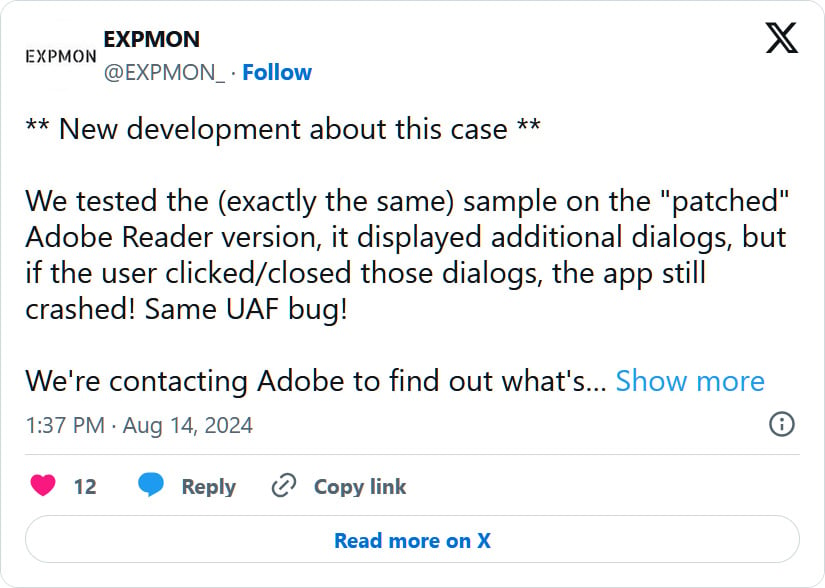
After Li disclosed the flaw to Adobe, a security update was released in August. However, the update did not fix the flaw and could still be triggered after closing various dialogs.
"We tested the (exactly the same) sample on the "patched" Adobe Reader version, it displayed additional dialogs, but if the user clicked/closed those dialogs, the app still crashed! Same UAF bug!," tweeted the EXPMON X account.
Yesterday, Adobe released a new security update that fixes the bug, now tracked as CVE-2024-41869.
Li will be releasing details on how the bug was detected on EXPMON's blog and further technical information in an upcoming Check Point Research report.
RIP Matrix | Farewell my friend ![]()
Hope you enjoyed this news post.
Thank you for appreciating my time and effort posting news every single day for many years.
2023: Over 5,800 news posts | 2024 (till end of August): 3,792 news posts
- Ha91 and alf9872000
-

 2
2



3175x175(CURRENT).thumb.jpg.b05acc060982b36f5891ba728e6d953c.jpg)
Recommended Comments
There are no comments to display.
Join the conversation
You can post now and register later. If you have an account, sign in now to post with your account.
Note: Your post will require moderator approval before it will be visible.